How to Setup OpenClaw Pairing Code: A Simple Guide

In today's rapidly evolving digital landscape, artificial intelligence (AI) has transcended from a futuristic concept to an indispensable tool for businesses and developers worldwide. From automating customer service with intelligent chatbots to revolutionizing data analysis and content generation, the applications of AI are boundless. The backbone of this revolution, for many organizations, lies in the strategic integration of API AI capabilities. These Application Programming Interfaces allow developers to harness sophisticated AI models and services without needing to build them from scratch, significantly accelerating innovation and time to market. However, as the reliance on these powerful external services grows, so does the complexity of managing their access securely and efficiently. This introduces critical challenges related to authentication, authorization, and the perennial task of robust API key management.
The ease with which one can how to use AI API directly correlates with the security and simplicity of its access mechanisms. Traditional API keys, while functional, present inherent vulnerabilities. If compromised, an API key can grant unauthorized access to sensitive data, incur unexpected usage costs, and potentially disrupt services. This necessitates a more advanced approach to securing API interactions, especially in environments where multiple AI services are consumed across various applications and teams.
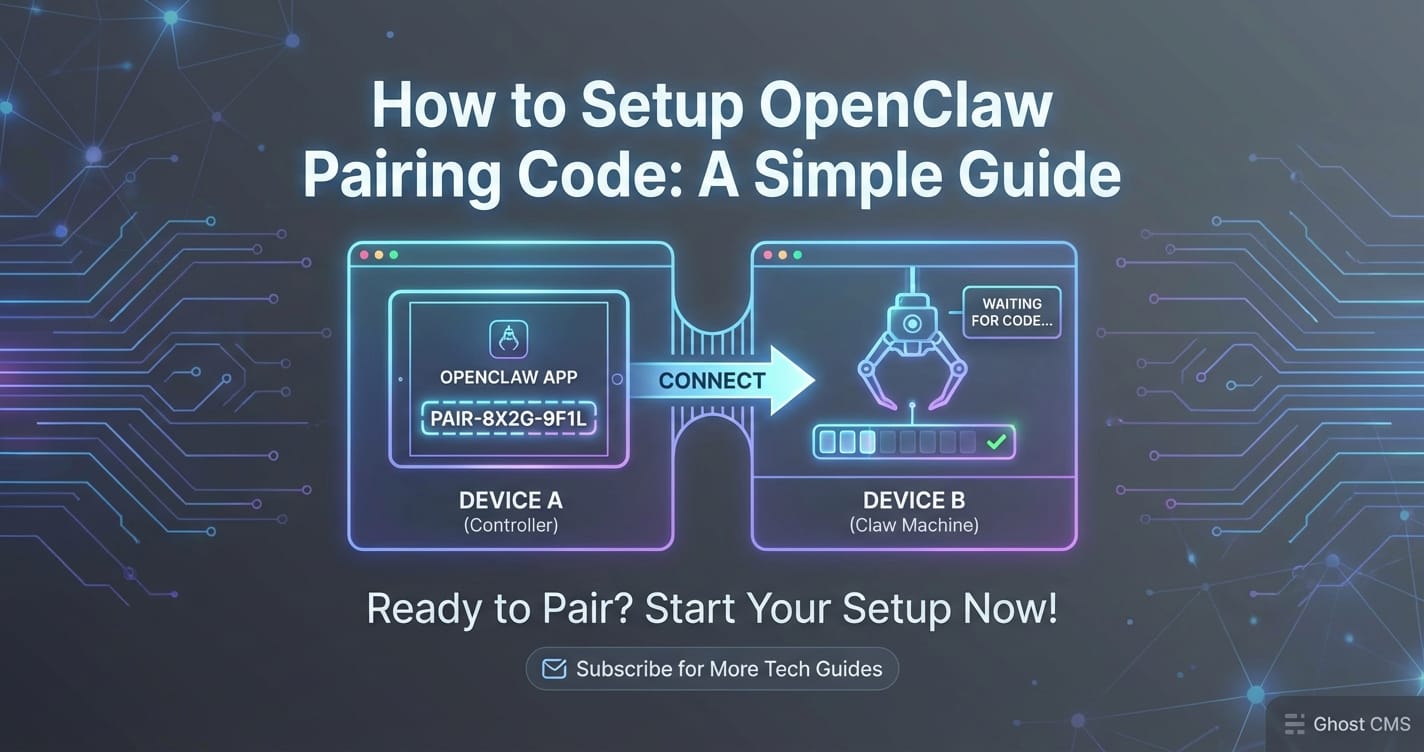
This comprehensive guide delves into "OpenClaw Pairing Code," an innovative concept designed to elevate the security posture of your API AI integrations. Think of it as a sophisticated layer of abstraction over your raw API keys, offering enhanced control, traceability, and resilience against common security threats. We will walk you through a detailed, step-by-step process on how to set up, implement, and manage OpenClaw Pairing Codes within your projects. Our aim is to demystify this powerful security feature, ensuring that you can confidently leverage advanced AI capabilities while maintaining the highest standards of security and operational efficiency. By the end of this guide, you will possess a clear understanding of OpenClaw Pairing Codes, their benefits, and the practical knowledge required to integrate them seamlessly into your development workflow, thereby mastering a crucial aspect of modern API key management and transforming how to use AI API effectively and securely.
Chapter 1: Understanding the Landscape of AI APIs and Inherent Security Challenges
The proliferation of AI capabilities has been largely driven by the availability of specialized API AI services. These APIs act as gateways to complex machine learning models, offering functionalities like natural language processing (NLP), computer vision, speech recognition, and generative AI. Developers can integrate these services into their applications with relative ease, transforming ordinary software into intelligent systems capable of understanding, reasoning, and creating.
What is an API AI?
At its core, an API AI is a set of defined requests and responses that allows applications to communicate with an AI model hosted by a service provider. Instead of running a large, resource-intensive model locally, developers can send data to the API, and the API will return the processed results. For example, a sentiment analysis API might receive a text string and return a score indicating whether the sentiment is positive, negative, or neutral. A generative AI API, on the other hand, might take a prompt and generate human-like text or images. This abstraction allows developers to focus on application logic rather than the intricate details of model training and deployment.
The benefits of integrating AI into applications via APIs are manifold:
- Accelerated Development: Pre-built, pre-trained models drastically reduce development time and effort.
- Cost-Effectiveness: Eliminates the need for expensive hardware, specialized AI talent for model development, and continuous model maintenance.
- Scalability: Providers handle the underlying infrastructure, allowing applications to scale AI usage seamlessly with demand.
- Access to Cutting-Edge Models: Developers gain access to the latest and most advanced AI research and models without needing to implement them from scratch.
- Focus on Core Business: Teams can dedicate more resources to their unique value proposition rather than reinventing AI capabilities.
Common types of AI APIs span a wide range of functionalities:
- Natural Language Processing (NLP): Sentiment analysis, entity recognition, text summarization, language translation, chatbot interfaces.
- Computer Vision: Object detection, image classification, facial recognition, optical character recognition (OCR).
- Speech Technologies: Speech-to-text, text-to-speech, voice assistants.
- Generative AI: Text generation (for articles, code, creative content), image synthesis, video creation.
- Predictive Analytics: Forecasting, recommendation engines, fraud detection.
These diverse capabilities empower developers to build sophisticated applications that were once the exclusive domain of large research institutions. The ease of access, however, comes with a significant responsibility: securing the interaction.
The Inherent Security Challenges in AI API Integration
While the convenience of how to use AI API is undeniable, the integration process introduces several critical security challenges. These challenges are not unique to AI APIs but are amplified by the sensitive nature of the data often processed by AI models and the potential for abuse.
- Data Privacy and Confidentiality: Many AI applications process sensitive information, such as personal data, proprietary business insights, or confidential communications. Sending this data to a third-party API requires absolute assurance that it will be handled securely, in compliance with regulations like GDPR or HIPAA, and not used for unauthorized purposes. A compromised API key could expose this data to malicious actors.
- Unauthorized Access and Abuse: The most immediate threat is unauthorized access. If an API key falls into the wrong hands, attackers can use it to impersonpersonate your application, make costly requests, or even exfiltrate data. This can lead to significant financial losses (due to fraudulent usage charges), reputational damage, and legal repercussions.
- Key Exposure: API keys are often long strings of characters that grant programmatic access. They can be accidentally exposed in various ways:
- Hardcoding in client-side code: If an API key is embedded directly into front-end JavaScript or mobile app code, it can be easily extracted by anyone inspecting the code.
- Insecure environment variables: Storing keys in plain text environment variables on a server, especially if the server is compromised, poses a risk.
- Version control systems: Accidentally committing API keys to public or even private Git repositories is a common mistake.
- Logs and network traffic: Keys can inadvertently appear in application logs or be intercepted if API calls are not made over HTTPS.
- Lack of Granular Control: Traditional API keys often grant broad permissions. If a single key is used across multiple services or different parts of an application, a compromise means the attacker gains access to everything. This "all or nothing" approach makes it difficult to limit the blast radius of a security incident.
- Complexity of Rotation and Revocation: When an API key is suspected of being compromised, it must be rotated or revoked immediately. In complex systems with numerous integrations, identifying all instances where a key is used, replacing it, and ensuring no downtime can be a cumbersome and error-prone process.
Why Secure API Key Management is Paramount
Given these challenges, robust API key management is not merely a best practice; it is a fundamental requirement for any organization leveraging API AI. Effective management strategies are crucial for:
- Minimizing Security Risks: Proactive measures reduce the likelihood of key compromise and the severity of potential breaches.
- Ensuring Compliance: Adherence to data protection regulations and industry standards often mandates strict access control and audit trails.
- Controlling Costs: Preventing unauthorized API usage directly impacts operational expenditure.
- Maintaining Business Continuity: Secure keys mean uninterrupted service and reliable application performance.
- Building Trust: Demonstrating a commitment to security enhances user trust and protects brand reputation.
The need for more sophisticated authentication mechanisms beyond simple, static API keys has become evident. This is precisely where the concept of "OpenClaw Pairing Code" emerges as a crucial innovation. It addresses many of these pain points by offering a dynamic, time-limited, and context-aware approach to authenticating API access, thereby bolstering your overall API key management strategy and making how to use AI API safer and more reliable.
Chapter 2: The Core Concept of OpenClaw Pairing Code
As we've established, while API AI offers incredible power, the methods of securing access to these services have often lagged behind, leaving organizations vulnerable. The "OpenClaw Pairing Code" represents a significant leap forward in addressing these security concerns, particularly in the realm of API key management. It's designed to enhance the security posture of your integrations, offering a more resilient and flexible alternative to traditional, static API keys.
What Exactly is an OpenClaw Pairing Code?
Imagine an OpenClaw Pairing Code not as a direct replacement for your primary API key, but as a temporary, encrypted, and highly contextual access token. It acts as an intermediary, a kind of single-use or time-limited "pass" that your application presents to the API AI service instead of the master API key. This pass is generated on-demand and is bound by specific parameters, effectively limiting its power and lifespan.
In essence, an OpenClaw Pairing Code is:
- Temporary: It has a defined validity period, after which it automatically expires, rendering it useless. This significantly reduces the window of opportunity for attackers if the code is compromised.
- Contextual: It can be configured with specific permissions, scopes, and even IP address restrictions. For instance, a pairing code might only grant access to a specific NLP service for text summarization, from a particular server IP, and only for the next hour.
- Encrypted/Hashed: While the exact implementation might vary, the underlying process for generating and validating these codes involves cryptographic techniques to ensure their integrity and prevent tampering.
- Session-Based (often): In many implementations, it can be tied to an active user or application session, meaning its validity is contingent on the health and authenticity of that session.
Think of it like this: your primary API key is akin to the master key to your entire office building. You wouldn't hand that master key to everyone who needs to enter a single room for a short meeting. Instead, you'd issue them a temporary access card, programmed only for that specific room, for a limited time. The OpenClaw Pairing Code functions as that temporary access card for your API AI interactions.
Why It's Needed: Enhancing Security Beyond Simple API Keys
The necessity for OpenClaw Pairing Codes stems directly from the limitations and vulnerabilities inherent in traditional API key usage. Here's why it's a critical component for modern API key management:
- Reduced Risk of Key Compromise: With a pairing code, your primary, high-privilege API key never leaves your secure environment or is directly transmitted in every API request. This significantly lowers the attack surface. Even if a pairing code is intercepted, its limited scope and lifespan mitigate the damage.
- Improved Access Control and Granularity: Instead of a single key granting broad access, pairing codes allow for fine-grained permissions. You can issue different codes for different microservices, teams, or even specific functions within an API AI service. This principle of least privilege is fundamental to robust security.
- Easier Revocation and Rotation: If a pairing code is suspected to be compromised, it can be instantly revoked without impacting other operations or requiring a complete overhaul of your primary API key. Its inherent short lifespan also means automatic rotation, reducing the manual burden of API key management.
- Enhanced Auditability: Each pairing code generation and usage can be logged with specific metadata (who generated it, for what purpose, its scope, etc.), providing a clear audit trail for security monitoring and compliance.
- Protection Against Insider Threats: By restricting the direct exposure of master keys, pairing codes can help guard against malicious or accidental misuse by internal personnel.
How It Ties Into Best Practices for API Key Management
The OpenClaw Pairing Code model seamlessly integrates with and elevates existing best practices for API key management:
- Principle of Least Privilege: Pairing codes enforce this by allowing you to grant only the necessary permissions for a specific task or service.
- Key Isolation: Your master API keys can remain isolated in secure vaults or secrets managers, only being accessed by a dedicated service responsible for generating pairing codes.
- Dynamic Access: Instead of static, long-lived credentials, pairing codes promote dynamic, on-demand access, aligning with zero-trust security models.
- Automated Rotation: The time-limited nature of pairing codes inherently introduces automated rotation, a crucial aspect of reducing the risk window.
- Audit and Monitoring: The generation and usage of pairing codes provide rich data for logging, monitoring, and anomaly detection.
By adopting OpenClaw Pairing Codes, you transform how to use AI API from a potentially risky endeavor into a highly secure and controlled operation. This foundational understanding is crucial before we delve into the practical steps of setting up and implementing these codes. The following table provides a succinct comparison between traditional API keys and the enhanced security offered by OpenClaw Pairing Codes, illustrating their role in modern API key management.
| Feature | Traditional API Key | OpenClaw Pairing Code |
|---|---|---|
| Lifespan | Long-lived, often static | Short-lived, time-limited, or session-bound |
| Permissions | Often broad access to services/resources | Granular, configurable to specific scopes/actions |
| Exposure Risk | High, if compromised, attacker has full access | Low, limited blast radius if compromised due to expiry/scope |
| Rotation | Manual, disruptive, infrequent | Automated (due to expiry), less disruptive revocation |
| Revocation | Manual, often requires reissuing a new master key | Instantaneous for individual codes, no impact on master key |
| Storage | Requires secure storage (secrets manager, env vars) | Generated on-demand, less critical to persistently store |
| Auditability | Basic usage logs, difficult to trace specific purposes | Detailed logs of generation, purpose, and usage |
| Ease of Management | Simpler for small projects, complex at scale | More complex initial setup, simpler long-term management |
| Ideal Use Case | Low-security contexts, initial development | High-security environments, production systems, multi-team projects |
This comparison highlights why shifting towards a pairing code model is not just an option but a necessary evolution for secure and scalable API key management when dealing with sensitive API AI integrations.
Chapter 3: Pre-requisites for Setting Up OpenClaw Pairing Code
Before you can dive into generating and implementing OpenClaw Pairing Codes, it’s essential to ensure your environment is properly configured and that you have a foundational understanding of the necessary components. This preparatory phase is crucial for a smooth setup process and effective API key management.
1. Account Creation and Platform Access
First and foremost, you'll need an active account with the hypothetical platform that provides the OpenClaw service. This platform is where you will manage your primary API AI keys and generate the derived OpenClaw Pairing Codes.
- Platform Registration: If you don't already have one, register for an account. This typically involves providing an email address, setting up a password, and potentially verifying your identity.
- API AI Service Subscription: Ensure your account is subscribed to the specific API AI services you intend to use (e.g., a Generative AI service, an NLP service, or a Vision API). Without an active subscription, you won't have a primary API key to secure with OpenClaw.
- Access to the OpenClaw Dashboard/Portal: Locate the OpenClaw or security management section within your platform's dashboard. This is where you'll initiate the pairing code generation process. Familiarize yourself with the layout and available options.
2. Basic Understanding of API Concepts
While this guide aims to be comprehensive, a basic grasp of how APIs work will greatly assist you.
- What is an API? Understand that an API (Application Programming Interface) allows different software applications to communicate with each other. For API AI, it means your application sends requests to the AI model and receives responses.
- HTTP Methods: Be familiar with common HTTP methods like GET (retrieve data), POST (send data), PUT (update data), and DELETE (remove data). Most API AI interactions will primarily use POST for sending inputs and GET for retrieving results.
- Request/Response Structure: Understand that API interactions typically involve sending data in a structured format (like JSON or XML) and receiving responses in a similar format.
- Authentication: Grasp the concept that APIs require authentication to verify your identity and ensure you have permission to access the requested resources. This is where API keys and, subsequently, OpenClaw Pairing Codes come into play.
3. Network Requirements and Security Considerations
Your network environment plays a vital role in secure API AI integration.
- Secure Connection (HTTPS/SSL/TLS): Always ensure that all your API calls are made over HTTPS (HTTP Secure). This encrypts the communication channel between your application and the API AI service, protecting your pairing codes and data from eavesdropping. Any reputable API AI provider will enforce HTTPS.
- Firewall Rules: If your application runs within a restricted network environment (e.g., a corporate data center or a private cloud), you might need to configure firewall rules to allow outbound connections to the API AI endpoint. Check the documentation of your API AI provider for specific IP ranges or domain names to whitelist.
- Egress Filtering: Implement egress filtering on your network to restrict outbound connections to only necessary endpoints. This adds another layer of security, preventing your systems from communicating with malicious external sources.
4. Developer Tools and Environment Setup
To implement and test the OpenClaw Pairing Code, you'll need a functioning development environment.
- Programming Language Environment: Choose your preferred programming language (Python, Node.js, Java, Go, C#, etc.) and ensure its runtime environment is correctly set up.
- IDE/Code Editor: Have an Integrated Development Environment (IDE) or a capable code editor (e.g., VS Code, PyCharm, IntelliJ IDEA) ready.
- Terminal/Command Line Interface: You’ll need access to a terminal or command line for running scripts, installing packages, and possibly making cURL requests for testing.
- HTTP Client Libraries: Ensure you have appropriate HTTP client libraries installed for your chosen language (e.g.,
requestsfor Python,axiosornode-fetchfor Node.js). - Version Control System: Use a version control system like Git to manage your code. Be extremely careful not to commit your actual API keys or even pairing codes directly into your repository.
- Secrets Management Solution: For robust API key management, especially with your primary keys, consider using a dedicated secrets management solution. This could be a cloud-native service (like AWS Secrets Manager, Azure Key Vault, Google Secret Manager), an open-source tool (e.g., HashiCorp Vault), or simply secure environment variables in a production-grade setup. This is crucial for storing your master API keys that will be used to generate OpenClaw Pairing Codes.
5. Existing API AI Keys (and Initial API Key Management)
Before you can create pairing codes, you must have at least one primary, master API key for the API AI service you intend to secure.
- Locate Your Master API Key: Log into your API AI provider's dashboard and retrieve your main API key. This key often has full access to your account's services, so handle it with extreme care.
- Secure Storage of Master Key: This master key should never be hardcoded directly into your application. Instead, store it securely. Best practices for API key management dictate using:
- Environment Variables: For local development and simpler deployments, storing keys as environment variables (
export API_KEY="your_key") is a common approach. - Secrets Management Services: For production environments, these are highly recommended. They provide centralized, encrypted storage, access control, and audit capabilities.
- Environment Variables: For local development and simpler deployments, storing keys as environment variables (
- Understand Its Permissions: Familiarize yourself with the permissions granted by your master API key. OpenClaw Pairing Codes will derive their power from this master key, but with reduced scope.
By carefully addressing these pre-requisites, you lay a strong foundation for securely integrating API AI services using OpenClaw Pairing Codes. This diligent preparation not only streamlines the setup process but also reinforces your overall API key management strategy, ensuring that how to use AI API is done in the most secure and efficient manner possible.
XRoute is a cutting-edge unified API platform designed to streamline access to large language models (LLMs) for developers, businesses, and AI enthusiasts. By providing a single, OpenAI-compatible endpoint, XRoute.AI simplifies the integration of over 60 AI models from more than 20 active providers(including OpenAI, Anthropic, Mistral, Llama2, Google Gemini, and more), enabling seamless development of AI-driven applications, chatbots, and automated workflows.
Chapter 4: Step-by-Step Guide to Generating Your OpenClaw Pairing Code
With your environment prepared and your understanding of API AI and its security challenges solidified, we can now proceed to the core process: generating your OpenClaw Pairing Code. This process typically occurs within the secure environment of your API AI provider's platform, ensuring your primary API keys remain protected.
Step 4.1: Accessing the OpenClaw Dashboard/Portal
The first step is to navigate to the dedicated section for managing OpenClaw Pairing Codes within your API AI provider's platform.
- Log In: Access your API AI provider's portal using your administrative credentials.
- Locate Security/API Management Section: Look for menu items or dashboard widgets labeled "API Keys," "Security Settings," "Access Management," or specifically "OpenClaw Management." The exact path will vary by provider.
- Enter OpenClaw Interface: Click on the relevant link to enter the OpenClaw configuration interface. Here, you should see options to view existing pairing codes (if any), generate new ones, or manage related settings.
Self-reflection: The design of this interface is crucial for ease of API key management. A well-designed portal would intuitively guide users through the process, minimizing potential errors.
Step 4.2: Initiating the Pairing Process
Once in the OpenClaw interface, you'll typically find an option to "Generate New Pairing Code" or "Initiate Pairing."
- Select "Generate New Code": Click on this option to begin the process.
- Choose Target API AI Service: If your provider offers multiple API AI services (e.g., a Generative Text API and a Vision API), you might be prompted to select which service this pairing code will grant access to. This ensures the code is context-specific from the outset.
- Input Existing API Key (Securely): This is a critical step. The OpenClaw system needs to know which master API key it is deriving permissions from. You will usually be asked to:
- Select from a list of pre-configured master keys: If you've previously stored your master keys in the platform's secrets manager. This is the most secure method.
- Paste your master API key temporarily: Some systems might require you to paste the key, which it then hashes or encrypts internally before discarding the raw key. Ensure this interaction happens over HTTPS and that the key is not stored permanently by the UI.
- Reference a key ID: If your platform uses key IDs for master keys, you might just select the ID.
Important Note: At no point should your master API key be exposed or stored client-side in plain text. The OpenClaw system uses it internally to establish trust and derive the pairing code's capabilities. This step underscores the importance of robust API key management for your primary credentials.
Step 4.3: Configuring Pairing Parameters
This is where you define the specific characteristics and restrictions of your OpenClaw Pairing Code. Granular control here is vital for maintaining the principle of least privilege.
- Define Scope and Permissions:
- Service Scope: Which specific API AI functionalities should this code allow? For a Generative AI API, this could be "text generation," "code generation," or "fine-tuning access." You should select only the necessary permissions.
- Resource Scope: Does the code need access to all models or only specific ones (e.g.,
model-Abut notmodel-B)? - Action Scope: Can it only
readdata, or alsowrite(e.g., upload training data)?
- Set Validity Period (Lifespan):
- Expiration Date/Time: Specify exactly when the pairing code should become invalid. This could range from minutes for a single-use script to days or weeks for a persistent application component.
- Session-based: Some advanced implementations might allow the code to expire after a certain period of inactivity or upon a specific event.
- Recommendation: Always choose the shortest practical validity period. This is a cornerstone of good security and API key management.
- IP Address Whitelisting:
- Restrict by Source IP: Configure the pairing code to be valid only when requests originate from specific IP addresses or IP ranges. This is highly recommended for server-side applications, adding a critical layer of network security.
- Example: If your application server has a static IP of
203.0.113.45, you would whitelist203.0.113.45/32.
- Rate Limiting (Optional):
- Some platforms might allow you to set specific rate limits (e.g., X requests per minute) directly on the pairing code, providing an additional layer of control and cost management.
- Descriptive Name/Label:
- Assign a clear, descriptive name to your pairing code (e.g., "Frontend Chatbot Prod," "Data Analyst Script – Monthly Report"). This is crucial for API key management and auditing, especially when dealing with many codes.
Table: OpenClaw Pairing Code Configuration Options
| Configuration Option | Description | Security/Management Impact |
|---|---|---|
| Service Scope | Which specific API AI services it can access | Limits exposure; principle of least privilege |
| Action Scope | What operations it can perform (read, write, generate) | Fine-grained control, prevents unauthorized actions |
| Validity Period | How long the code remains active | Reduces risk window if compromised, promotes automatic rotation |
| IP Whitelisting | Restricts usage to specific IP addresses | Network-level security, prevents use from unknown locations |
| Rate Limiting | Sets usage limits (e.g., requests per minute) | Cost control, prevents abuse/DDoS-like attacks |
| Description/Label | Human-readable name for identification and auditing | Essential for API key management and incident response |
Step 4.4: Generating the Code
Once all parameters are configured to your satisfaction, you'll click the "Generate" or "Create" button.
- Code Generation: The system will process your configuration and generate the unique OpenClaw Pairing Code. This code will typically be a long, alphanumeric string.
- Display of Code: The generated code will be displayed on your screen. Crucially, for security reasons, many platforms will only display this code ONCE. You must copy it immediately. If you navigate away or close the window without copying it, you might need to revoke it and generate a new one.
- Record Key Information: Along with the code itself, note down its expiration date, scope, and any other relevant details in a secure location (e.g., your secrets manager).
Structure of a hypothetical OpenClaw Pairing Code (example, not functional): ocpc_g7Fh4JqL2pN8sM1tV6wX9yZ3aBcD5eFgHiJkL0mN2oP4qR6sT8uVwXyZ0aB2c4d6e8fG This code is designed to be opaque, its meaning only understood by the OpenClaw system.
Step 4.5: Securely Storing and Managing the Pairing Code
Generating the code is only half the battle; securing it is paramount for effective API key management.
- Immediate Secure Storage:
- Secrets Manager: For production environments, immediately store the OpenClaw Pairing Code in a dedicated secrets management solution (e.g., HashiCorp Vault, AWS Secrets Manager).
- Environment Variables: For development or smaller deployments, store it as an environment variable (
OPENCLAW_PAIRING_CODE=ocpc_...) in your runtime environment. - Avoid Hardcoding: Never hardcode the pairing code directly into your source code.
- Avoid Version Control: Never commit the pairing code to Git or any other version control system. Use
.gitignoreto prevent accidental commits of environment files.
- Regular Review and Rotation: Even though pairing codes have a limited lifespan, it's good practice to:
- Monitor Usage: Regularly check the logs for the pairing code to ensure it's being used as expected and within its defined scope.
- Proactive Rotation: For long-running applications, implement a mechanism to automatically request and use a new pairing code before the old one expires. This can be integrated into your application's lifecycle or CI/CD pipeline.
- Revocation Planning: Understand how to revoke a pairing code instantly should you suspect it has been compromised or is no longer needed. This typically involves going back to the OpenClaw dashboard and selecting the "Revoke" option for the specific code.
By following these detailed steps, you can confidently generate OpenClaw Pairing Codes, establish robust API key management practices, and ensure that how to use AI API within your applications is done with an enhanced layer of security and control. The next chapter will focus on integrating these generated codes into your actual application code.
Chapter 5: Implementing OpenClaw Pairing Code in Your Applications
Once you have successfully generated your OpenClaw Pairing Code and stored it securely, the next crucial step is to integrate it into your application. This involves modifying your existing API AI calls to use the pairing code instead of, or in conjunction with, your traditional API key. This section will guide you through the practical aspects of how to use AI API with OpenClaw.
Step 5.1: Choosing Your API AI Integration Method
Before diving into code modifications, consider how your application typically interacts with API AI services.
- SDKs (Software Development Kits): Many API AI providers offer language-specific SDKs that simplify interactions. These SDKs often abstract away HTTP requests and provide convenient methods for calling AI functionalities.
- Direct HTTP Requests: If an SDK isn't available or you prefer more direct control, you'll make HTTP requests (using libraries like
requestsin Python orfetchin JavaScript) to the API endpoints.
Regardless of the method, the core principle remains the same: the OpenClaw Pairing Code needs to be included in the authentication header of your API requests.
Step 5.2: Modifying API Calls to Use the Pairing Code
The most common way to pass an OpenClaw Pairing Code is via the Authorization HTTP header, typically as a Bearer token. This is a standard practice for many modern APIs.
Let's look at pseudocode examples for common programming languages:
Example in Python (using requests library):
import os
import requests
import json
# --- Securely retrieve your OpenClaw Pairing Code ---
# In a real application, this would come from a secrets manager or environment variable.
openclaw_pairing_code = os.environ.get("OPENCLAW_PAIRING_CODE")
if not openclaw_pairing_code:
raise ValueError("OPENCLAW_PAIRING_CODE environment variable not set.")
# --- Define the API AI endpoint and payload ---
# Replace with your actual API AI service endpoint
api_url = "https://api.example-ai.com/v1/generate_text"
payload = {
"model": "text-davinci-003", # Example model
"prompt": "Write a short poem about the future of AI.",
"max_tokens": 150
}
# --- Construct the headers, including the OpenClaw Pairing Code ---
headers = {
"Content-Type": "application/json",
"Authorization": f"Bearer {openclaw_pairing_code}" # THIS IS THE KEY CHANGE
}
# --- Make the API request ---
try:
response = requests.post(api_url, headers=headers, data=json.dumps(payload))
response.raise_for_status() # Raise an exception for HTTP errors (4xx or 5xx)
# Process the response
ai_response = response.json()
print("AI Generated Text:")
print(ai_response.get("choices")[0].get("text"))
except requests.exceptions.HTTPError as err:
print(f"HTTP error occurred: {err}")
print(f"Response content: {response.text}")
except requests.exceptions.ConnectionError as err:
print(f"Connection error occurred: {err}")
except requests.exceptions.Timeout as err:
print(f"Timeout error occurred: {err}")
except requests.exceptions.RequestException as err:
print(f"An unexpected error occurred: {err}")
Example in JavaScript (Node.js using node-fetch):
const fetch = require('node-fetch'); // Install: npm install node-fetch
require('dotenv').config(); // Install: npm install dotenv to load .env files
// --- Securely retrieve your OpenClaw Pairing Code ---
const openClawPairingCode = process.env.OPENCLAW_PAIRING_CODE;
if (!openClawPairingCode) {
throw new Error("OPENCLAW_PAIRING_CODE environment variable not set.");
}
// --- Define the API AI endpoint and payload ---
const apiUrl = "https://api.example-ai.com/v1/analyze_sentiment"; // Example endpoint
const payload = {
"text": "The new product launch was an absolute disaster, a total failure."
};
// --- Construct the headers, including the OpenClaw Pairing Code ---
const headers = {
"Content-Type": "application/json",
"Authorization": `Bearer ${openClawPairingCode}` // THIS IS THE KEY CHANGE
};
// --- Make the API request ---
async function analyzeSentiment() {
try {
const response = await fetch(apiUrl, {
method: 'POST',
headers: headers,
body: JSON.stringify(payload)
});
if (!response.ok) {
const errorText = await response.text();
throw new Error(`HTTP error! status: ${response.status}, message: ${errorText}`);
}
const aiResponse = await response.json();
console.log("Sentiment Analysis Result:");
console.log(aiResponse);
} catch (error) {
console.error("An error occurred during sentiment analysis:", error);
}
}
analyzeSentiment();
Key Change Highlighted: The critical modification in both examples is the line Authorization: f"Bearer {openclaw_pairing_code}" or Authorization: \Bearer ${openClawPairingCode}`. This is **how to use AI API** with the OpenClaw Pairing Code for authentication. TheBearer` prefix is a standard convention indicating a token-based authentication scheme.
Step 5.3: Error Handling and Troubleshooting
Implementing OpenClaw Pairing Codes introduces new potential points of failure, primarily related to the code's validity and scope. Robust error handling is crucial.
- Expired Code (401 Unauthorized / 403 Forbidden): The most common issue. If your pairing code has passed its validity period, the API AI service will reject the request.
- Solution: Implement logic to check the expiration time of the pairing code before making a request. If it's expired or nearing expiration, initiate a process to request a new one from your OpenClaw management service.
- Invalid Scope/Permissions (403 Forbidden): If the pairing code was generated with limited permissions, and your application attempts an action outside that scope, the API will deny access.
- Solution: Review the OpenClaw configuration and ensure the pairing code has all the necessary permissions for the intended API AI calls.
- Incorrect Format (400 Bad Request / 401 Unauthorized): If the pairing code is malformed or the
Authorizationheader is not set correctly.- Solution: Double-check the code in your application and ensure the
Bearerprefix is correctly applied.
- Solution: Double-check the code in your application and ensure the
- Network Issues (Connection Errors/Timeouts): Standard network problems can also prevent successful API calls.
- Solution: Ensure your server can reach the API AI endpoint, check firewall rules, and verify DNS resolution.
- Troubleshooting Tips:
- Logs: Scrutinize your application logs and the API AI provider's logs (if accessible) for detailed error messages.
- Testing: Use tools like
curlor Postman to test API calls manually with the pairing code. This helps isolate whether the issue is with your application code or the pairing code itself. - Monitoring: Set up monitoring and alerting for API errors, especially
401and403responses, which indicate authentication or authorization failures related to your API key management.
Step 5.4: Integrating with Different AI Models and Unified API Platforms (XRoute.AI Mention)
The beauty of the OpenClaw Pairing Code approach, particularly when designed for broad compatibility, is its potential to streamline secure access across various API AI models and even different providers.
For developers looking to streamline their access to a multitude of Large Language Models (LLMs) from various providers, platforms like XRoute.AI offer a cutting-edge unified API platform. With XRoute.AI, you can manage access to over 60 AI models from more than 20 active providers through a single, OpenAI-compatible endpoint. This significantly simplifies how to use AI API across diverse models, such as GPT, Claude, Llama, and many others, without the complexity of managing multiple API connections and their respective authentication mechanisms.
If an OpenClaw-like system were universally adopted or if XRoute.AI were to integrate such a security layer, it would dramatically enhance API key management for multi-model, multi-provider AI solutions. Imagine generating a single OpenClaw Pairing Code that, through XRoute.AI's unified endpoint, could securely authenticate requests to various underlying LLMs, all with granular permissions and a limited lifespan. This approach would centralize and fortify your security posture, making low latency AI and cost-effective AI not just performant but also incredibly secure. XRoute.AI's focus on developer-friendly tools, high throughput, and scalability makes it an ideal partner for securely deploying intelligent solutions, especially when complemented by advanced access control mechanisms like OpenClaw Pairing Codes. It transforms the challenge of how to use AI API effectively into a seamless, secure, and highly manageable experience.
By abstracting away the complexities of individual API AI provider authentication, a platform like XRoute.AI can potentially serve as a central point for validating and routing OpenClaw Pairing Codes to the correct underlying AI service, further enhancing both security and operational efficiency. This vision highlights the future of API key management in an increasingly interconnected AI ecosystem.
Chapter 6: Advanced OpenClaw Features and Best Practices
Setting up and implementing OpenClaw Pairing Codes is a great start, but true security and operational efficiency come from continuous management and leveraging advanced features. This chapter explores sophisticated techniques and best practices to master your API key management strategy with OpenClaw, ensuring your API AI integrations remain secure and robust over time.
6.1. Rotation and Revocation of Pairing Codes
The ephemeral nature of OpenClaw Pairing Codes is a key security advantage. However, understanding how to actively manage their lifecycle is crucial.
- Automated Rotation:
- Principle: While pairing codes expire automatically, implementing a proactive rotation strategy means your application requests a new code before the current one expires.
- Mechanism: Your application or an intermediary service should be responsible for detecting an approaching expiration (e.g., 10 minutes before expiry) and making a request to the OpenClaw management API (using your secure master API key) for a new pairing code. The old code is then gracefully retired.
- Benefits: This prevents service interruptions due to expired codes, further reduces the window of exposure for any single code, and minimizes manual intervention. It's a cornerstone of advanced API key management.
- Instant Revocation:
- Scenario: If you suspect a pairing code has been compromised, or if an associated application/service is decommissioned, you must revoke it immediately.
- Process: Access the OpenClaw dashboard, locate the specific pairing code by its descriptive name, and initiate the "Revoke" action. The system should invalidate the code instantly.
- Impact: Revocation should only affect that specific pairing code, leaving all other active codes and your master API key untouched. This isolation is a major advantage over revoking a primary API key.
- Audit Trail: Every revocation should be logged with details (who, when, why) for audit purposes.
6.2. Monitoring Usage and Detecting Anomalies
Effective API key management extends beyond just issuing keys; it includes vigilant monitoring.
- Real-time Logging: Configure your applications and the OpenClaw service to log every API call made with a pairing code. This includes:
- Timestamp
- Source IP address
- OpenClaw Pairing Code ID (if available)
- Target API AI service/endpoint
- HTTP status code of the response
- Usage Analytics: Utilize the monitoring tools provided by your API AI provider and OpenClaw platform to track usage patterns. Look for:
- Spikes in Usage: Unusually high request volumes for a specific pairing code.
- Geographical Anomalies: Requests originating from unexpected geographic locations.
- Unauthorized Access Attempts: Frequent
401or403errors for a particular code, which could indicate brute-force attempts. - Deviations from Baseline: Any usage pattern that significantly differs from the expected behavior of the application using the code.
- Alerting: Set up automated alerts for suspicious activities. For example, an alert could trigger if:
- A pairing code receives
Xfailed authentication attempts withinYminutes. - Usage for a specific code exceeds
Zrequests per hour, particularly for codes with rate limits. - A pairing code is used from an IP address not on its whitelist.
- A pairing code receives
- Benefits: Proactive monitoring helps detect and respond to security incidents quickly, preventing larger breaches and ensuring the integrity of your API AI interactions.
6.3. Integration with CI/CD Pipelines
Automating the lifecycle of OpenClaw Pairing Codes can significantly improve security and developer productivity.
- Dynamic Code Provisioning:
- Integrate the OpenClaw management API into your CI/CD pipeline.
- When deploying a new application or service, the pipeline can automatically request a new, appropriately scoped OpenClaw Pairing Code.
- This newly generated code is then injected into the deployment environment (e.g., as an environment variable in a Kubernetes pod or a serverless function) rather than being manually configured.
- Automated Rotation and Decommissioning:
- Pipelines can also be configured to trigger the rotation of pairing codes on a schedule or to automatically revoke codes when an application/service is deprecated or removed.
- Secrets Injection: Use secure secrets injection tools (e.g., HashiCorp Vault Agent, Kubernetes Secrets CSI Driver, cloud-native secret managers) within your CI/CD process to safely deliver pairing codes to running applications without ever writing them to disk or exposing them in logs.
- Benefits: This approach ensures consistency, reduces human error, enhances the speed of deployment, and significantly strengthens API key management at scale.
6.4. Auditing and Logging
Comprehensive auditing is essential for compliance, incident response, and continuous security improvement.
- Immutable Logs: Ensure that all actions related to OpenClaw Pairing Codes (generation, configuration changes, usage, revocation) are logged in an immutable, tamper-proof system.
- Detailed Records: Logs should include:
- User/System responsible for the action.
- Timestamp.
- Specific action performed (e.g.,
create_pairing_code,update_scope,revoke_code). - Parameters of the action (e.g.,
scope_changed_from: A to B,expiration_set_to: datetime). - Source IP address of the action.
- Regular Audits: Periodically review these audit logs to ensure compliance, identify any unauthorized activities, or spot potential misconfigurations.
- Benefits: Provides a clear paper trail for forensic analysis in case of a breach, helps meet regulatory requirements, and supports continuous security posture refinement.
6.5. Security Implications and Continuous API Key Management
The adoption of OpenClaw Pairing Codes doesn't eliminate the need for vigilance but rather elevates your API key management to a more sophisticated level.
- Master Key Protection is Paramount: Remember that OpenClaw Pairing Codes are derived from your master API AI keys. The security of these master keys remains foundational. Continue to protect them with the utmost care, using dedicated secrets managers and limiting access to highly privileged accounts.
- Educate Your Team: Ensure all developers and operations personnel understand the principles of OpenClaw, the importance of granular permissions, and the secure handling of pairing codes. Knowledge is a powerful security tool.
- Stay Informed: The landscape of API AI and security is constantly evolving. Stay updated on the latest security best practices, vulnerabilities, and new features offered by your API AI provider and OpenClaw platform.
- Regular Security Assessments: Conduct regular security audits and penetration tests on your applications and infrastructure to identify potential weaknesses in your OpenClaw implementation or overall API key management.
Table: Best Practices for OpenClaw Pairing Code Management
| Best Practice | Description | Impact on Security and Operations |
|---|---|---|
| Shortest Lifespan | Configure pairing codes with the shortest possible validity periods. | Minimizes exposure window if compromised. |
| Least Privilege Scope | Grant only the exact permissions needed for a specific task/service. | Limits potential damage from a compromised code. |
| IP Whitelisting | Restrict usage to known, trusted IP addresses. | Prevents unauthorized external access. |
| Automated Rotation | Implement mechanisms to automatically refresh codes before expiry. | Prevents downtime, reduces manual overhead, enhances security. |
| Real-time Monitoring | Track code usage, detect anomalies, and set up alerts. | Early detection of security incidents and misuse. |
| Secrets Management | Store master keys and pairing codes in dedicated secret vaults. | Protects credentials from exposure in code, logs, or version control. |
| CI/CD Integration | Automate code generation, injection, and decommissioning. | Boosts efficiency, consistency, and security at scale. |
| Comprehensive Auditing | Maintain immutable logs of all code lifecycle events and usage. | Facilitates compliance, forensics, and continuous improvement. |
| Team Education | Train developers on secure handling and best practices. | Fosters a security-first culture, reduces human error. |
By embracing these advanced features and best practices, your organization can move beyond basic API key management to a truly secure, automated, and resilient system for integrating API AI into your applications. This comprehensive approach ensures that how to use AI API becomes synonymous with robust security and operational excellence.
Conclusion
The journey through setting up and managing OpenClaw Pairing Codes reveals a critical evolution in how we approach the security of our API AI integrations. In an era where AI capabilities are no longer a luxury but a necessity, the ability to harness these powerful services securely is paramount. Traditional API keys, while foundational, present inherent vulnerabilities that demand a more sophisticated defense mechanism. OpenClaw Pairing Codes step into this breach, offering a dynamic, granular, and time-bound solution that significantly elevates your security posture.
We've explored the landscape of API AI, understood the critical security challenges associated with direct API key usage, and then delved into the core concept of OpenClaw Pairing Codes as a robust answer to these challenges. By acting as temporary, context-specific passes, these codes reduce the risk of key compromise, enhance access control, and simplify the burdensome task of revocation and rotation, thus transforming your entire API key management strategy.
The step-by-step guide provided a practical roadmap, from setting up your environment and understanding crucial pre-requisites to the meticulous process of generating a pairing code with specific scopes and lifespans. We then demonstrated how to use AI API with these codes by integrating them into application code, ensuring that your requests are authenticated securely. Crucially, we also highlighted the role of unified API platforms like XRoute.AI in streamlining access to diverse LLMs, illustrating how advanced security mechanisms can perfectly complement such cutting-edge tools to deliver low latency AI and cost-effective AI with uncompromised security. XRoute.AI's developer-friendly tools simplify the complexity of managing multiple models, making it an ideal environment where sophisticated API key management strategies can truly shine, allowing you to focus on building intelligent solutions rather than grappling with integration intricacies.
Finally, we delved into advanced features and best practices, emphasizing automated rotation, vigilant monitoring, seamless CI/CD integration, and comprehensive auditing. These elements are not just add-ons; they are vital components of a mature and resilient API key management system that ensures your API AI usage is not only productive but also rigorously secure.
Embracing OpenClaw Pairing Codes is more than just adopting a new security feature; it's a commitment to best practices in the evolving world of AI development. It empowers developers and organizations to confidently leverage the full potential of artificial intelligence, knowing that their access is controlled, auditable, and protected against the myriad of threats that loom in the digital realm. By integrating these practices, you secure your present AI applications and build a resilient foundation for future innovations, making "how to use AI API" a truly secure and efficient endeavor.
Frequently Asked Questions (FAQ)
Q1: What is an OpenClaw Pairing Code?
An OpenClaw Pairing Code is a temporary, time-limited, and highly configurable access token designed to enhance the security of your API AI integrations. It acts as an intermediary credential, allowing your applications to authenticate with AI services without directly exposing your more powerful, long-lived master API keys. It typically has a defined lifespan, specific permissions (scope), and can be restricted to certain IP addresses.
Q2: Is OpenClaw Pairing Code a replacement for my primary API key?
No, an OpenClaw Pairing Code is not a replacement for your primary API AI key. Instead, it serves as a derived, secondary credential. Your master API key, which grants broad access to your account, is used by the OpenClaw management system to generate these temporary pairing codes. The goal is to minimize the direct exposure and use of your master key in your applications, thus improving your overall API key management security.
Q3: How often should I rotate my OpenClaw Pairing Codes?
OpenClaw Pairing Codes have a pre-defined validity period (lifespan) set during their generation, after which they automatically expire. The best practice is to set the shortest practical lifespan for your specific use case. For continuously running applications, it is highly recommended to implement an automated rotation mechanism in your application or CI/CD pipeline. This system should proactively request and switch to a new pairing code before the current one expires, ensuring continuous service and minimizing the window of exposure for any single code.
Q4: Can I use OpenClaw Pairing Code with any API AI service?
The availability and compatibility of OpenClaw Pairing Codes depend on the API AI provider. This guide assumes a hypothetical provider offers such a service. If your provider supports a similar mechanism (e.g., scoped API keys, short-lived access tokens, or integration with secrets managers that issue temporary credentials), the principles of secure API key management discussed here would still apply. For platforms like XRoute.AI, which provide a unified API for numerous LLMs, the potential for a single, securely managed token to control access across multiple models through a unified endpoint offers a highly efficient way to how to use AI API securely.
Q5: What should I do if I lose my OpenClaw Pairing Code?
If you lose an OpenClaw Pairing Code (i.e., you failed to copy it securely after generation, or it was accidentally deleted), you should immediately access your OpenClaw management dashboard. If the code was not securely stored and is thus irrecoverable, the safest approach is to revoke the lost code (if it was copied and potentially exposed, even accidentally) and then generate a completely new one. Since pairing codes have a limited lifespan and specific scopes, the risk associated with a lost code is generally lower than a lost master API key, but immediate action is always prudent as part of diligent API key management.
🚀You can securely and efficiently connect to thousands of data sources with XRoute in just two steps:
Step 1: Create Your API Key
To start using XRoute.AI, the first step is to create an account and generate your XRoute API KEY. This key unlocks access to the platform’s unified API interface, allowing you to connect to a vast ecosystem of large language models with minimal setup.
Here’s how to do it: 1. Visit https://xroute.ai/ and sign up for a free account. 2. Upon registration, explore the platform. 3. Navigate to the user dashboard and generate your XRoute API KEY.
This process takes less than a minute, and your API key will serve as the gateway to XRoute.AI’s robust developer tools, enabling seamless integration with LLM APIs for your projects.
Step 2: Select a Model and Make API Calls
Once you have your XRoute API KEY, you can select from over 60 large language models available on XRoute.AI and start making API calls. The platform’s OpenAI-compatible endpoint ensures that you can easily integrate models into your applications using just a few lines of code.
Here’s a sample configuration to call an LLM:
curl --location 'https://api.xroute.ai/openai/v1/chat/completions' \
--header 'Authorization: Bearer $apikey' \
--header 'Content-Type: application/json' \
--data '{
"model": "gpt-5",
"messages": [
{
"content": "Your text prompt here",
"role": "user"
}
]
}'
With this setup, your application can instantly connect to XRoute.AI’s unified API platform, leveraging low latency AI and high throughput (handling 891.82K tokens per month globally). XRoute.AI manages provider routing, load balancing, and failover, ensuring reliable performance for real-time applications like chatbots, data analysis tools, or automated workflows. You can also purchase additional API credits to scale your usage as needed, making it a cost-effective AI solution for projects of all sizes.
Note: Explore the documentation on https://xroute.ai/ for model-specific details, SDKs, and open-source examples to accelerate your development.