OpenClaw ClawJacked Fix: Easy Troubleshooting Steps
The digital landscape is a dynamic realm where systems operate at breakneck speeds, processing torrents of data and executing complex operations. Yet, even the most robust architectures are not immune to unforeseen challenges. One such vexing predicament, which we'll refer to in the context of our hypothetical OpenClaw system, is the "ClawJacked" state. Imagine a critical system that, without warning, becomes unresponsive, sluggish, or behaves erratically—a state akin to a machine whose gears have seized, or whose control has been inexplicably hijacked. This isn't just an inconvenience; it can lead to significant operational disruptions, data inconsistencies, and a frustrating halt to productivity.
This comprehensive guide is designed to serve as your ultimate resource for diagnosing, troubleshooting, and ultimately fixing the "ClawJacked" phenomenon within your OpenClaw environment. Whether OpenClaw represents a sophisticated automation platform, a data processing pipeline, a robotic control system, or a critical software application, the principles of systematic troubleshooting remain universally applicable. We will delve into common symptoms, explore potential root causes, and walk through a series of structured steps—from initial diagnosis to advanced solutions—to restore your system to optimal health. Our journey will also emphasize crucial aspects such as performance optimization, cost optimization, and secure API key management, ensuring that your OpenClaw system not only recovers but thrives efficiently and securely.
The goal is not merely to offer a quick fix but to empower you with the knowledge and methodologies to approach future system anomalies with confidence and precision. By understanding the underlying mechanisms and applying a methodical approach, you can transform a daunting "ClawJacked" crisis into a manageable technical challenge, ultimately enhancing the reliability and resilience of your OpenClaw operations.
Understanding the "ClawJacked" Phenomenon
Before we can effectively fix a "ClawJacked" system, we must first understand what it entails. While "OpenClaw" and "ClawJacked" are illustrative terms for a generic system and its malfunction, they represent a broad spectrum of real-world issues that can plague any complex software or hardware setup.
What Does "ClawJacked" Mean? Defining the Symptoms
A system is "ClawJacked" when it deviates significantly from its expected, healthy operational state. The symptoms can manifest in various ways, often indicating different underlying problems:
- Unresponsiveness or Freezing: The system or specific components stop responding to input, API calls, or commands. User interfaces freeze, background processes halt, or scheduled tasks fail to initiate.
- Severe Performance Degradation: Operations that typically complete in milliseconds now take seconds or minutes. Latency spikes dramatically, throughput drops, and resource utilization (CPU, memory) might appear abnormally high or low for the perceived workload. This is a clear indicator of a need for performance optimization.
- Erroneous Outputs or Data Corruption: The system produces incorrect results, processes data inaccurately, or corrupts stored information. This can range from subtle calculation errors to widespread data integrity issues.
- Frequent Crashes or Restarts: Applications or the entire system repeatedly crash, leading to service interruptions and potential data loss. These might be soft crashes (application-level) or hard crashes (kernel panics, system reboots).
- Resource Exhaustion: The system consistently runs out of memory, disk space, or CPU cycles, even under what should be normal load. This can trigger cascades of failures across dependent services.
- Network Connectivity Issues: Despite the underlying network appearing stable, the OpenClaw system struggles to communicate with external services, databases, or internal components. This could manifest as timeouts or connection refused errors.
- Unauthorized Activity or Security Alerts: Suspicious log entries, unexpected network traffic, or security warnings might indicate a compromise or an unauthorized process interfering with normal operations. While not always a "ClawJacked" state in the performance sense, it represents a loss of control.
Potential Root Causes: Peeling Back the Layers
Understanding the symptoms is the first step; identifying the root cause is the diagnostic challenge. "ClawJacked" states rarely emerge from a single, isolated incident but are often the culmination of several interacting factors.
- Software Bugs and Glitches:
- Logic Errors: Flaws in the code's logic can lead to incorrect processing, infinite loops, or unexpected states that halt execution.
- Memory Leaks: Applications that fail to release memory after use can gradually consume all available RAM, leading to performance degradation and eventual crashes.
- Concurrency Issues: Race conditions, deadlocks, or improper synchronization in multi-threaded or distributed systems can cause processes to freeze or produce incorrect results.
- Resource Mismanagement: Inefficient use of file handles, network connections, or database connections can exhaust system limits.
- Configuration Errors and Misconfigurations:
- Incorrect Parameters: Wrong values in configuration files (e.g., database connection strings, API endpoints, timeout settings) can prevent services from starting or operating correctly.
- Environment Mismatches: Differences between development, staging, and production environments (e.g., differing library versions, OS settings) can lead to unexpected behavior when code is deployed.
- Missing Dependencies: Required libraries, drivers, or external executables might be absent or incorrectly installed, causing runtime errors.
- Resource Contention and System Overload:
- CPU Bottlenecks: A single process consuming excessive CPU, or too many processes competing for limited CPU cores, can bring the entire system to a crawl.
- I/O Bottlenecks: Slow disk access (e.g., worn-out SSDs, heavily fragmented HDDs) or network I/O saturation can significantly impede data-intensive operations.
- Memory Pressure: When physical RAM is exhausted, the system resorts to swap space, which is dramatically slower, leading to severe slowdowns.
- Network Congestion: High traffic, faulty network hardware, or misconfigured network devices can prevent data from reaching or leaving the OpenClaw system in a timely manner.
- External Service Failures and API Issues:
- Third-Party API Downtime: If OpenClaw relies on external APIs (e.g., payment gateways, data providers, AI models), their unavailability or degraded performance can "ClawJack" OpenClaw's own operations.
- Rate Limiting: Exceeding the allowed request rate for an external API can lead to temporary blocks, halting OpenClaw's ability to communicate.
- Authentication and Authorization Errors: Expired credentials, revoked API key management issues, or incorrect permissions can prevent successful interaction with external services.
- Network Latency to External Services: Geographically distant APIs or poor network routing can introduce delays, impacting responsiveness.
- Security Breaches and Unauthorized Access:
- Malware or Viruses: Malicious software can consume resources, corrupt data, or interfere with legitimate processes.
- Compromised Credentials: Stolen API key management credentials or user passwords can allow attackers to gain control, modify configurations, or inject harmful code.
- Denial-of-Service (DoS) Attacks: Malicious traffic overwhelming the system's network or processing capabilities.
The Impact of a "ClawJacked" State
The consequences of a "ClawJacked" system extend beyond mere technical frustration:
- Operational Disruptions and Downtime: Direct loss of service, affecting users, customers, or internal business processes.
- Data Integrity Issues: Corrupted databases, inconsistent records, or irreversible data loss, leading to compliance risks and financial penalties.
- Financial Losses: Lost revenue due to unavailable services, increased operational costs from incident response, and potential penalties for service level agreement (SLA) breaches.
- Reputational Damage: Erosion of trust among users and stakeholders, impacting brand image and customer loyalty.
- Reduced Productivity: Engineers and teams diverted from development to urgent troubleshooting, slowing down innovation and feature delivery.
- Challenges for Performance Optimization: A constantly "ClawJacked" system makes it impossible to achieve desired performance metrics, impacting user experience and efficiency.
- Increased Operational Costs: Inefficient resource usage during a "ClawJacked" state can lead to higher cloud bills or infrastructure expenses, highlighting the importance of cost optimization.
Understanding these symptoms, causes, and impacts lays the groundwork for a systematic approach to fixing and preventing future "ClawJacked" incidents.
Initial Diagnosis and Pre-Troubleshooting Steps
When your OpenClaw system enters a "ClawJacked" state, panic is a natural first reaction. However, a calm, methodical approach is paramount. The initial diagnosis focuses on gathering immediate clues and verifying fundamental system health, much like a first responder assessing a situation.
1. The "Power Cycle" Equivalent: Restarting Components (Judiciously)
In many cases, a simple restart can resolve transient issues by clearing temporary states, resetting network connections, and re-initializing services. However, this should be done judiciously:
- Identify the Scope: Do you need to restart the entire server, a specific application, a container, or just a service? Start with the smallest affected component.
- Check Dependencies: Before restarting, ensure that dependent services will not be negatively impacted. For example, restarting a database without ensuring its clients can reconnect gracefully can cause wider outages.
- Document the Action: Note what was restarted, when, and the immediate effect. This is crucial for pattern analysis later.
- Why it works: Restarts can resolve memory leaks (by freeing all memory), clear network connection issues, or fix applications stuck in a bad state.
- Caveat: A restart is a temporary fix if the underlying problem persists. If the system immediately "ClawJacks" again, you need to dig deeper.
2. Checking System Logs: The Digital Breadcrumbs
Logs are invaluable for understanding what a system was doing leading up to a failure. They are the primary source of truth for post-mortem analysis.
- Identify Relevant Logs:
- System Logs (OS level):
/var/log/syslog(Linux), Event Viewer (Windows). Look for hardware errors, kernel panics, or system-level service failures. - Application Logs: Logs generated by OpenClaw itself or its individual components. These might be in a specific directory (e.g.,
/var/log/openclaw/), or managed by logging frameworks like Log4j, Winston, or Serilog. - Web Server Logs: Apache access/error logs, Nginx access/error logs if OpenClaw has a web interface or API.
- Database Logs: PostgreSQL, MySQL, MongoDB logs can reveal slow queries, connection issues, or corruption warnings.
- Container/Orchestration Logs: If using Docker, Kubernetes, etc., check container logs and pod events (
kubectl logs,docker logs).
- System Logs (OS level):
- What to Look For:
- Error Messages: Specific error codes, stack traces, "Failed," "Error," "Critical" keywords.
- Warnings: Messages indicating potential problems, even if not critical failures (e.g., "resource limit exceeded," "deprecated feature use").
- Timestamps: Correlate log entries with the time the "ClawJacked" state began.
- Repeated Patterns: Are certain errors or warnings occurring frequently?
- Resource Depletion: Messages indicating memory exhaustion, disk full, or too many open files.
- Tools:
grep,awk,tail -f,less,journalctl(for systemd). For centralized logging, use tools like ELK Stack (Elasticsearch, Logstash, Kibana), Splunk, Datadog, or Sumo Logic, which make analysis significantly easier.
3. Monitoring Resource Usage: The Vital Signs
Resource utilization metrics provide a snapshot of your system's health. Abnormal spikes or sustained high usage can point directly to the problem.
- CPU Usage:
- Tools:
top,htop,vmstat,sar(Linux); Task Manager (Windows); Cloud provider dashboards (AWS CloudWatch, Azure Monitor, GCP Monitoring). - Look For: A single process consuming 100% CPU, or overall CPU utilization consistently near maximum, indicating a CPU bottleneck or a runaway process.
- Tools:
- Memory Usage:
- Tools:
free -h,htop,vmstat(Linux); Task Manager (Windows). - Look For: High "used" memory, low "free" memory, significant "swap" usage (indicating memory pressure and slow performance). Identify processes consuming large amounts of RAM.
- Tools:
- Disk I/O:
- Tools:
iostat,df -h(Linux); Resource Monitor (Windows). - Look For: High disk read/write rates, high disk utilization percentage, or disk full conditions. This can indicate heavy logging, database activity, or application storing large temporary files.
- Tools:
- Network I/O:
- Tools:
netstat,ss,iftop,nload(Linux); Resource Monitor (Windows). - Look For: High network traffic, especially unexpected outbound traffic (potential compromise), or a large number of open connections that are stuck (deadlocks, unclosed connections).
- Tools:
- Cloud Specific Metrics: If running on a cloud platform, leverage their native monitoring tools for instance health, disk IOPS, network packets in/out, database connection counts, etc.
4. Verifying Network Connectivity: The Communication Lifeline
Many "ClawJacked" states stem from an inability to communicate with internal or external services.
- Ping Test:
ping <IP_address_or_hostname>to check basic reachability to external services, databases, or other OpenClaw components. - Traceroute/Tracert:
traceroute <IP_address_or_hostname>(Linux/macOS),tracert <IP_address_or_hostname>(Windows) to identify where network packets are getting stuck or experiencing high latency. - Netstat/SS:
netstat -tulnporss -tulnpto see which ports are open and listening, and which connections are established or in aWAITstate. This helps verify if OpenClaw is listening on its expected ports and if connections to its dependencies are active. - DNS Resolution: Use
nslookupordigto confirm that hostnames are resolving correctly to IP addresses. Incorrect DNS can cause services to fail silently. - Firewall Rules: Check if any firewall rules (OS-level, network security groups, WAFs) are blocking necessary inbound or outbound traffic.
5. Confirming Dependencies and Prerequisites: The Foundation
OpenClaw, like most complex systems, relies on a stack of dependencies.
- Software Versions: Ensure that all required libraries, runtimes (e.g., Python, Java, Node.js), and external binaries are installed at their correct, compatible versions. Version mismatches are a frequent source of obscure errors.
- Environment Variables: Verify that all necessary environment variables (e.g.,
PATH,JAVA_HOME,API_KEY) are correctly set for the OpenClaw process. - File Permissions: Incorrect file or directory permissions can prevent OpenClaw from reading configuration files, writing logs, or accessing data.
- Disk Space: A full disk can lead to a multitude of issues, from application crashes to failed updates. Use
df -hto check disk usage. - System Time Synchronization: Ensure system time (NTP) is synchronized. Time differences can cause issues with authentication, logging, and distributed transactions.
By systematically going through these initial diagnostic steps, you can often quickly pinpoint the area of the problem or, at the very least, gather sufficient information to proceed with more targeted, in-depth troubleshooting.
Deep Dive into Common ClawJacked Fixes
With initial diagnostics complete, we can now delve into specific categories of fixes that address the most frequent causes of "ClawJacked" states. Each area demands a careful, structured approach.
3.1. Configuration Review and Correction
Misconfigurations are insidious because they can appear as functional until a specific edge case or load condition is met. They are often the stealthy culprit behind many "ClawJacked" incidents.
- Identify Common Configuration Pitfalls:
- Hardcoded Values: Directly embedding IP addresses, port numbers, or credentials instead of using environment variables or configuration files, making changes difficult and error-prone.
- Inconsistent Environments: Configuration differences between development, staging, and production environments. A setting that works locally might break in production.
- Incorrect Resource Limits: Insufficient memory allocations, CPU shares, or connection pool sizes that lead to resource exhaustion under load.
- Wrong API Endpoints or Credentials: Pointing to an incorrect API gateway or using expired/invalid API key management tokens.
- Network Configuration Errors: Incorrect subnet masks, gateway addresses, or DNS server entries preventing communication.
- Timeouts: Setting overly aggressive timeouts for external API calls or database queries, causing operations to fail prematurely.
- Best Practices for Configuration Management:
- Centralized Configuration: Use configuration management tools (e.g., Ansible, Puppet, Chef) or dedicated configuration services (e.g., Consul, Etcd, AWS Systems Manager Parameter Store) to manage configurations across environments.
- Environment Variables: Prefer environment variables for sensitive data (like API keys) and environment-specific settings.
- Version Control: Treat configuration files as code. Store them in Git or similar version control systems. This allows for change tracking, rollbacks, and peer review.
- Validation: Implement schema validation for configuration files (YAML, JSON) to catch syntax errors or invalid values before deployment.
- Documentation: Clearly document each configuration parameter, its purpose, default value, and potential impact.
- Principle of Least Privilege: Configure services with the minimum necessary permissions to perform their function.
- Correction Strategy:
- Isolate the Change: If possible, identify the last configuration change made before the "ClawJacked" state appeared.
- Rollback: Revert to a known good configuration. Version control makes this straightforward.
- Test Systematically: Change one configuration parameter at a time and observe its effect. Avoid making multiple changes simultaneously.
- Validate on Staging: Always test configuration changes in a staging environment that mirrors production as closely as possible.
3.2. Dependency Management and Updates
Outdated or incompatible dependencies are a silent killer, often introducing subtle bugs or security vulnerabilities that can trigger "ClawJacked" scenarios.
- Outdated Libraries/Drivers:
- Older versions might contain known bugs that have been fixed in newer releases.
- They might lack support for newer operating system features or hardware, leading to instability.
- Security vulnerabilities in outdated libraries are a common attack vector.
- Compatibility Issues:
- Transitive Dependencies: A library you explicitly install might pull in other libraries (transitive dependencies) that conflict with other parts of your OpenClaw system.
- Runtime Environment: An application developed on Python 3.8 might behave unexpectedly or fail on Python 3.6 due to syntax changes or missing features.
- Operating System: Libraries compiled for one OS version might not work correctly on another.
- The Role of Package Managers:
- Modern package managers (npm for Node.js, pip for Python, Maven/Gradle for Java, Composer for PHP, NuGet for .NET) are essential for managing dependencies.
- They help define explicit versions (
package.json,requirements.txt,pom.xml), resolve dependency conflicts, and handle installation. - Lock Files: Always use lock files (e.g.,
package-lock.json,yarn.lock,Pipfile.lock) to ensure consistent dependency resolution across all environments.
- Correction Strategy:
- Audit Dependencies: Generate a dependency tree for your OpenClaw application to see all direct and transitive dependencies and their versions.
- Check for Known Vulnerabilities: Use tools like
npm audit,pip-audit, or OWASP Dependency-Check to identify components with known security flaws. - Incremental Updates: Update dependencies incrementally, testing after each major version bump, rather than attempting a large-scale update all at once.
- Read Release Notes: Always review the release notes of new dependency versions for breaking changes, performance improvements, or bug fixes relevant to your "ClawJacked" issue.
- Rebuild and Redeploy: After updating dependencies, ensure a clean rebuild and redeployment of your OpenClaw application.
3.3. Resource Management and Performance Tuning (Performance Optimization)
A significant portion of "ClawJacked" incidents stems from resource exhaustion or inefficient resource utilization. Performance optimization is not just about speed; it's about stability and preventing the system from seizing up under load.
- Identifying Bottlenecks:
- Profiling Tools: Use application profilers (e.g., Java Flight Recorder, Python cProfile, Node.js V8 Inspector) to pinpoint functions or code blocks consuming the most CPU or memory.
- Database Query Analysis: Analyze slow queries using
EXPLAIN ANALYZE(SQL), database performance monitoring tools, or query logs. - Load Testing: Simulate production load to identify where the system breaks down or performance degrades.
- Strategies for Performance Optimization:
- Caching:
- Application-level cache: Store frequently accessed data in memory (e.g., Redis, Memcached) to avoid repeated database queries or computations.
- Content Delivery Networks (CDNs): Cache static assets (images, CSS, JS) closer to users, reducing load on your origin server and improving delivery speed.
- Database Caching: Leverage database-level caches for query results or frequently accessed tables.
- Load Balancing: Distribute incoming requests across multiple OpenClaw instances to prevent any single instance from becoming overwhelmed.
- Asynchronous Processing: Use message queues (e.g., RabbitMQ, Kafka, AWS SQS) for long-running or non-critical tasks. This allows the main application thread to remain responsive.
- Efficient Algorithms and Data Structures: Review critical code paths for algorithmic complexity. Sometimes, a change from O(n^2) to O(n log n) can make a dramatic difference.
- Database Optimization:
- Indexing: Create appropriate indexes on frequently queried columns to speed up data retrieval.
- Query Optimization: Refactor inefficient SQL queries, avoid
SELECT *, useJOINs efficiently. - Connection Pooling: Reuse database connections instead of establishing new ones for every request, reducing overhead.
- Memory Management:
- Garbage Collection Tuning: For languages like Java or Go, fine-tune garbage collector parameters to minimize pause times.
- Identify Memory Leaks: Regularly monitor memory usage and use profiling tools to find objects that are not being garbage collected.
- Data Structure Choice: Choose memory-efficient data structures.
- Scaling Considerations:
- Vertical Scaling: Increasing the resources (CPU, RAM) of a single server. Limited by hardware capabilities.
- Horizontal Scaling: Adding more servers or instances. Requires stateless applications and a load balancer. Kubernetes is excellent for managing horizontal scaling.
- Caching:
Here's a table summarizing common performance bottlenecks and their respective solutions:
| Bottleneck Category | Description | Common Symptoms | Performance Optimization Solutions |
|---|---|---|---|
| CPU | Excessive computation, inefficient code, infinite loops | High CPU usage (near 100%), slow response times | Code profiling to identify hot spots, algorithmic optimization, caching computation results, asynchronous processing, horizontal scaling (adding more CPU cores/servers). |
| Memory | Memory leaks, large data structures, insufficient RAM | High RAM usage, excessive swap activity, OutOfMemoryError | Memory profiling to detect leaks, optimize data structures, garbage collection tuning, increasing allocated RAM, reducing unnecessary data loading. |
| I/O (Disk) | Slow disk reads/writes, frequent file operations | High disk utilization, slow database queries, application freezes | Use faster storage (SSDs, NVMe), optimize database indexing, configure proper caching, batch writes, avoid frequent small file operations, ensure sufficient disk space. |
| I/O (Network) | High network latency, bandwidth saturation, slow API calls | Slow external service responses, connection timeouts, high network traffic | Optimize network configurations, reduce data transfer size, utilize CDNs, implement efficient API usage (batching requests), use connection pooling, choose geographically closer endpoints. |
| Database | Slow queries, locking, connection limits, poor schema | High database CPU/memory, long query execution times, connection errors | Query optimization (indexing, EXPLAIN plans), connection pooling, denormalization for read-heavy workloads, proper transaction management, database sharding/replication, use ORMs efficiently. |
| Concurrency | Race conditions, deadlocks, inefficient locks | Application freezes, inconsistent data, intermittent errors | Proper use of mutexes, semaphores, atomic operations, lock-free data structures, review concurrency patterns, avoid global locks, ensure proper resource release. |
| External APIs | Third-party service downtime, rate limits, latency | ClawJacked on external calls, error responses, delays |
Implement circuit breakers, retry mechanisms (with exponential backoff), caching API responses, respect rate limits, monitor external service health, consider API gateway solutions. (e.g., XRoute.AI for LLM APIs) |
3.4. Data Integrity and Corruption Checks
Data corruption is a severe form of "ClawJacked" state, leading to incorrect decisions, system failures, and potential legal ramifications.
- Database Issues:
- Corrupted Tables/Indexes: Power outages, hardware failures, or software bugs can corrupt database files.
- Transaction Failures: Incomplete transactions can leave data in an inconsistent state.
- Schema Drift: Changes to the database schema that are not properly propagated or managed can cause applications to fail.
- Deadlocks: Two or more transactions waiting for each other to release locks, leading to system freezes.
- File System Corruption:
- Physical disk errors, improper shutdowns, or software bugs can damage the file system, making files unreadable or corrupt.
- Correction Strategy:
- Regular Backups: Implement a robust backup strategy (daily, weekly, transactional logs) with tested recovery procedures. Store backups off-site.
- Database Health Checks:
- Use
fsckfor file systems (after unmounting). - Utilize database-specific tools like
REPAIR TABLE(MySQL),pg_dumpandpg_restore(PostgreSQL), or MongoDB'svalidatecommand. - Monitor for database errors (checksum mismatches, integrity violations).
- Use
- Transaction Management: Ensure all data modifications are wrapped in atomic transactions (ACID properties) to guarantee consistency.
- Data Validation: Implement strong data validation at the application level to prevent invalid data from entering the system.
- Replication: Use database replication (master-slave, multi-master) to ensure data availability and provide redundancy.
By systematically addressing configuration errors, managing dependencies, optimizing performance, and ensuring data integrity, you can resolve a significant majority of "ClawJacked" scenarios and build a more resilient OpenClaw system.
XRoute is a cutting-edge unified API platform designed to streamline access to large language models (LLMs) for developers, businesses, and AI enthusiasts. By providing a single, OpenAI-compatible endpoint, XRoute.AI simplifies the integration of over 60 AI models from more than 20 active providers(including OpenAI, Anthropic, Mistral, Llama2, Google Gemini, and more), enabling seamless development of AI-driven applications, chatbots, and automated workflows.
Advanced Troubleshooting for Persistent "ClawJacked" States
When standard troubleshooting methods fail, it's time to elevate your approach. Persistent "ClawJacked" states often point to deeper, more intricate problems that require specialized tools and expertise.
4.1. Security Audits and Vulnerability Checks
A "ClawJacked" system might not just be broken; it could be compromised. Security incidents can manifest as performance degradation, unusual behavior, or data manipulation.
- Identifying Security-Related "ClawJacked" Symptoms:
- Unexpected Outbound Network Traffic: Your OpenClaw system making connections to unknown external IPs.
- New, Unknown Processes: Malicious processes running alongside legitimate ones, consuming resources or exfiltrating data.
- Modified Files: Critical system or application files changed without authorization.
- Elevated Privileges: Accounts or processes gaining higher permissions than expected.
- Unusual Log Entries: Failed login attempts from suspicious IPs, changes in authentication mechanisms.
- Performing a Security Audit:
- Vulnerability Scanning: Use tools like Nessus, OpenVAS, or Qualys to scan your OpenClaw system and its underlying infrastructure for known vulnerabilities.
- Penetration Testing: Engage security experts to simulate attacks and identify weaknesses.
- Configuration Review: Check security-related configurations, such as firewall rules, access control lists (ACLs), and user permissions.
- Malware Scan: Run antivirus/anti-malware scans on the host system.
- Log Analysis for Anomalies: Beyond error messages, look for patterns indicative of attacks, such as brute-force attempts, SQL injection attempts, or unauthorized access.
- Hardening Measures:
- Regular Patching: Keep the OS, OpenClaw application, and all dependencies updated with the latest security patches.
- Principle of Least Privilege: Grant users and services only the minimum necessary permissions.
- Multi-Factor Authentication (MFA): Enforce MFA for all administrative access.
- Network Segmentation: Isolate critical OpenClaw components on separate network segments.
- Intrusion Detection/Prevention Systems (IDS/IPS): Deploy systems to monitor for and block malicious activity.
- Web Application Firewalls (WAFs): Protect web-facing OpenClaw components from common web exploits.
4.2. API and External Service Integration (Api Key Management)
Many modern systems, including OpenClaw, rely heavily on external APIs for various functionalities—from data enrichment and communication to leveraging cutting-edge AI models. Issues with these integrations, particularly regarding API key management, can easily lead to a "ClawJacked" state.
- Common API Integration Pitfalls:
- Rate Limit Exceedance: Making too many requests to an external API within a given timeframe, leading to temporary blocks or errors.
- Authentication Failures: Expired, revoked, or incorrect API keys/tokens.
- Network Issues: Latency or connectivity problems to the API provider.
- API Provider Downtime: The external service itself experiencing an outage.
- Breaking Changes: API provider making changes to their API (endpoints, request/response formats) without proper notice or backward compatibility.
- Incorrect Error Handling: OpenClaw not gracefully handling API errors (e.g., 4xx, 5xx responses), leading to application crashes or freezes.
- API Key Management Best Practices: API key management is critical for both security and functionality. Poor management can expose credentials, lead to unauthorized access, and cause service disruptions.
| Aspect | Best Practice | Rationale |
|---|---|---|
| Secure Storage | Use dedicated secrets management services (e.g., AWS Secrets Manager, HashiCorp Vault, Azure Key Vault) or environment variables. Avoid hardcoding keys in code or committing them to version control. | Prevents exposure of sensitive credentials, centralizes control. |
| Rotation | Regularly rotate API keys (e.g., every 90 days). Automate this process where possible. | Minimizes the impact of a compromised key; if a key is leaked, its lifespan is limited. |
| Least Privilege | Grant API keys only the minimum necessary permissions required for the specific task. | Limits the scope of damage if a key is compromised. |
| Granular Permissions | If an API allows, create keys with specific permissions rather than master keys. | Enhances security by restricting what a compromised key can do. |
| Access Control | Implement strict access control to who can retrieve or manage API keys within your organization. | Prevents unauthorized internal access to credentials. |
| Audit Trails | Log all access and usage of API keys. | Crucial for security monitoring, forensic analysis, and compliance. |
| Lifecycle Management | Establish clear procedures for generating, distributing, revoking, and decommissioning API keys. | Ensures keys are managed throughout their entire lifecycle, preventing orphaned or forgotten keys. |
| Monitoring | Monitor API key usage patterns for anomalies (e.g., unusual call volumes, calls from unexpected locations). | Detects potential misuse or compromise of keys in real-time. |
| Dedicated Keys | Use separate API keys for different applications, environments (dev, staging, prod), or even different microservices. | Isolates issues and prevents one compromised key from affecting multiple systems. |
| Encryption in Transit/Rest | Ensure API keys are encrypted when transmitted over networks (HTTPS) and when stored at rest. | Protects keys from interception and unauthorized access. |
- Troubleshooting API Integration Issues:Leveraging Unified API Platforms: Managing numerous API keys, handling varying rate limits, and dealing with diverse integration patterns for many external services (especially for large language models (LLMs), which OpenClaw might utilize) can become a significant source of "ClawJacked" situations. This is where a platform like XRoute.AI shines. XRoute.AI offers a unified API platform that provides a single, OpenAI-compatible endpoint to access over 60 AI models from more than 20 active providers. This dramatically simplifies API key management by centralizing access and abstracting away the complexities of integrating with multiple, disparate LLM APIs. For OpenClaw systems relying on AI capabilities, XRoute.AI ensures more robust and less "ClawJacked" AI integrations, contributing to smoother operations and reduced troubleshooting efforts.
- Verify API Key/Token: Double-check that the correct, unexpired API key is being used.
- Check API Documentation: Consult the external API's documentation for rate limits, error codes, and best practices.
- Test API Independently: Use tools like
curl, Postman, or Insomnia to make direct API calls, bypassing OpenClaw, to confirm the API itself is functional. - Monitor Network to API: Use
ping,tracerouteto assess connectivity and latency to the API endpoint. - Review API Provider Status Pages: Many providers have public status pages indicating outages or degraded performance.
- Implement Circuit Breakers and Retries: For resilience, integrate patterns like circuit breakers (to prevent cascading failures to an unresponsive API) and exponential backoff retries (for transient errors).
- Webhook Verification: If using webhooks, ensure OpenClaw's endpoint is reachable by the external service and can process incoming requests.
4.3. Leveraging Community and Support Resources
Sometimes, the problem isn't unique, and others have faced similar challenges. Tapping into collective knowledge is a powerful troubleshooting technique.
- Official Documentation: Thoroughly read OpenClaw's official documentation, FAQs, and troubleshooting guides.
- Community Forums and Online Groups: Search relevant forums (e.g., Stack Overflow, GitHub Issues, Reddit subreddits, project-specific mailing lists) for similar error messages or symptoms.
- Vendor Support: If OpenClaw is a commercial product or uses commercial components, engage with vendor support. Provide them with detailed logs, steps to reproduce, and environment specifics.
- Reproducing the Issue: The ability to consistently reproduce a "ClawJacked" state in a controlled environment (e.g., staging, development VM) is invaluable.
- Minimal Reproducible Example: Create the smallest possible code snippet or configuration that demonstrates the issue. This helps others help you.
- Isolation: Try to isolate the problematic component or configuration by removing non-essential parts of the system.
- Debugging Tools:
- Remote Debuggers: Attach a debugger to the OpenClaw process to step through code, inspect variables, and trace execution flow.
- Packet Sniffers: Tools like Wireshark can capture and analyze network traffic, revealing communication issues at a low level.
- System Tracing:
strace(Linux) can show system calls made by a process, helping to identify file access issues, network problems, or resource limits.
By methodically exploring security vectors, refining API integrations with secure API key management and potentially using unified platforms like XRoute.AI, and actively engaging with support resources, you can tackle even the most stubborn "ClawJacked" challenges.
Proactive Measures: Preventing Future "ClawJacked" Incidents
The best "ClawJacked" fix is the one you never need to perform. Proactive strategies focused on maintenance, monitoring, automation, and intelligent resource allocation are crucial for building a resilient OpenClaw system. This is where cost optimization also plays a significant role, as preventing issues often saves more than fixing them.
5.1. Regular Maintenance and Updates
Just like any complex machine, software systems require routine care.
- Scheduled Updates and Patch Management:
- Regularly update the operating system, OpenClaw application, and all its dependencies. This includes security patches and bug fixes.
- Establish a clear patching schedule and process (test in staging, roll out incrementally).
- Disk Cleanup and Health Checks:
- Periodically remove temporary files, old logs, and unused data to prevent disk space exhaustion.
- Monitor disk SMART data for impending hardware failures.
- Database Maintenance:
- Regularly optimize (defragment, rebuild indexes) and vacuum (PostgreSQL) databases.
- Archive old data to reduce database size and improve query performance.
- Configuration Audits: Periodically review configuration files to ensure they are still correct, optimized, and adhere to current best practices.
5.2. Robust Monitoring and Alerting Systems
Effective monitoring is your early warning system, allowing you to detect anomalies before they escalate into a full "ClawJacked" state.
- Comprehensive Metrics Collection:
- System Metrics: CPU, memory, disk I/O, network I/O.
- Application Metrics: Request rates, error rates, latency, active connections, queue depths, garbage collection metrics.
- Business Metrics: User sign-ups, transactions processed, key feature usage.
- Log Aggregation: Centralize logs from all OpenClaw components and their dependencies into a single platform (e.g., ELK Stack, Splunk, Datadog). This makes pattern analysis and correlation across services much easier.
- Health Checks: Implement automated health checks for all critical OpenClaw services and external dependencies. These can be simple HTTP endpoints or more complex transactional checks.
- Threshold-Based Alerting: Define clear thresholds for all critical metrics (e.g., CPU > 80% for 5 minutes, error rate > 5%, disk space < 10%).
- Anomaly Detection: Use machine learning-driven tools to identify deviations from normal behavior, which might indicate a nascent problem that simple thresholds would miss.
- Effective Alerting Channels: Configure alerts to notify the right people through appropriate channels (PagerDuty for critical alerts, Slack for warnings, email for informational). Avoid alert fatigue by fine-tuning thresholds.
- Dashboarding: Create clear, intuitive dashboards that visualize key metrics and give a quick overview of OpenClaw's health.
5.3. Automated Testing and Continuous Integration/Deployment (CI/CD)
Automation reduces human error and ensures that changes are introduced safely.
- Unit Tests: Verify individual components or functions of OpenClaw.
- Integration Tests: Ensure different OpenClaw components (or OpenClaw and external services) work correctly together.
- End-to-End Tests: Simulate user journeys to verify the entire system from a user's perspective.
- Performance/Load Tests: Regularly run load tests against OpenClaw to ensure it can handle expected traffic and identify performance regressions early.
- CI/CD Pipelines: Automate the entire process from code commit to deployment. This ensures that every change is tested, dependencies are consistently built, and deployments are predictable, significantly reducing the chance of introducing "ClawJacked" bugs.
- Infrastructure as Code (IaC): Manage your infrastructure (servers, networks, databases) using code (e.g., Terraform, CloudFormation, Ansible). This ensures consistency, reproducibility, and version control for your environment.
5.4. Strategies for Cost Optimization
Preventing "ClawJacked" scenarios through proactive measures often aligns directly with cost optimization. An unstable, inefficient system invariably costs more to operate and maintain.
- Resource Provisioning and Right-Sizing:
- Analyze Usage Patterns: Understand your OpenClaw system's resource requirements (CPU, RAM, disk, network) over time.
- Right-Size Instances: Don't over-provision resources. Use the smallest instance types that can comfortably handle your workload, especially in cloud environments.
- Auto-Scaling: Implement auto-scaling to dynamically adjust resources based on demand, scaling up during peak times and down during off-peak, to avoid paying for unused capacity.
- Serverless Architectures: Consider serverless functions (AWS Lambda, Azure Functions) for event-driven or intermittent OpenClaw tasks, as you only pay for actual execution time.
- Cloud Spend Analysis and Reserved Instances:
- Regularly review your cloud provider bills to identify areas of excessive spending.
- Purchase Reserved Instances or Savings Plans for predictable, long-running workloads to significantly reduce costs compared to on-demand pricing.
- Utilize Spot Instances for fault-tolerant or non-critical OpenClaw components.
- Efficient Data Storage and Transfer:
- Tiered Storage: Store infrequently accessed data in cheaper, archival storage tiers.
- Data Compression: Compress data where possible (e.g., logs, backups) to reduce storage footprint and transfer costs.
- Network Egress Costs: Be mindful of data transfer costs, especially between regions or out of the cloud provider's network. Optimize data locality.
- License Management: Track and optimize software licenses for any commercial components used by OpenClaw. Ensure you're not paying for unused licenses.
- API Usage Optimization:This is another area where XRoute.AI offers significant value. By providing a unified API platform with access to over 60 AI models from 20+ providers, XRoute.AI facilitates cost-effective AI integration. Developers using OpenClaw can easily switch between different LLM models or providers based on their specific pricing structures and performance needs without rewriting integration code. This flexibility allows for dynamic cost optimization, ensuring that your OpenClaw system leverages AI capabilities without incurring unnecessary expenses, thus preventing cost-related "ClawJacked" situations and making your operations more efficient and budget-friendly.
- Batching Requests: Where possible, combine multiple small API calls into a single, larger request to reduce per-request overhead.
- Caching API Responses: Cache responses from external APIs to reduce the number of actual calls, especially for static or slowly changing data.
- Choose Cost-Effective Providers: For services like LLMs, where OpenClaw might integrate, compare pricing across different providers.
Here's a table outlining key strategies for cost optimization in tech operations, particularly relevant for an OpenClaw system:
| Strategy Category | Description | Rationale | Impact on OpenClaw |
|---|---|---|---|
| Resource Right-Sizing | Continuously monitor and adjust computing resources (CPU, RAM, storage) to match actual OpenClaw workload demands, avoiding over-provisioning. | Eliminates wasteful spending on idle or underutilized resources. | Ensures OpenClaw runs on optimal infrastructure, reducing monthly cloud bills and improving efficiency. |
| Auto-Scaling | Implement mechanisms to automatically scale OpenClaw resources up or down based on real-time metrics (e.g., CPU utilization, queue depth). | Dynamically adjusts capacity to demand, paying only for resources when needed, and maintaining performance during peak loads. | OpenClaw remains performant during spikes without constant manual oversight or persistent over-provisioning. |
| Serverless Computing | Re-architect suitable OpenClaw components (e.g., event processors, batch jobs) to use serverless functions. | Pay-per-execution model drastically reduces costs for intermittent or event-driven workloads, as you don't pay for idle time. | Lower operational costs for specific OpenClaw tasks, reduced infrastructure management overhead. |
| Reserved Instances / Savings Plans | Commit to a certain level of resource usage (e.g., 1-year or 3-year commitment) with cloud providers for predictable OpenClaw workloads. | Significant discounts compared to on-demand pricing for stable, long-running services. | Substantially reduces the long-term infrastructure cost for the core, stable parts of OpenClaw. |
| Storage Tiering | Classify OpenClaw data by access frequency and criticality, storing less frequently accessed data in cheaper storage tiers (e.g., cold storage, archives). | Optimizes storage costs by matching data value with storage expense. | Reduces overall data storage costs, especially for logs, backups, or historical data generated by OpenClaw. |
| Network Egress Optimization | Minimize data transfer out of cloud regions or across different cloud providers, which often incurs higher costs. | Reduces expensive data egress charges by optimizing data locality and transfer patterns. | Lowers networking costs for OpenClaw when interacting with external services or transferring data between regions. |
| API Usage Optimization | Cache API responses, batch requests, implement smart retry logic, and select cost-effective API providers for external services (e.g., LLMs). | Reduces the number of billable API calls and allows for dynamic selection of providers based on cost/performance. | For AI-driven OpenClaw, significantly reduces costs associated with external API consumption, especially via platforms like XRoute.AI. |
| DevOps Automation | Automate CI/CD pipelines, infrastructure provisioning, and monitoring to reduce manual effort and human error. | Reduces operational overhead, speeds up development cycles, and minimizes downtime due to configuration errors, which are indirect cost savings. | Fewer "ClawJacked" incidents, faster recovery, and more efficient resource allocation for OpenClaw development and operations. |
By implementing these proactive strategies, your OpenClaw system will not only be more resilient against "ClawJacked" incidents but also operate more efficiently and cost-effectively, safeguarding your resources and ensuring long-term stability.
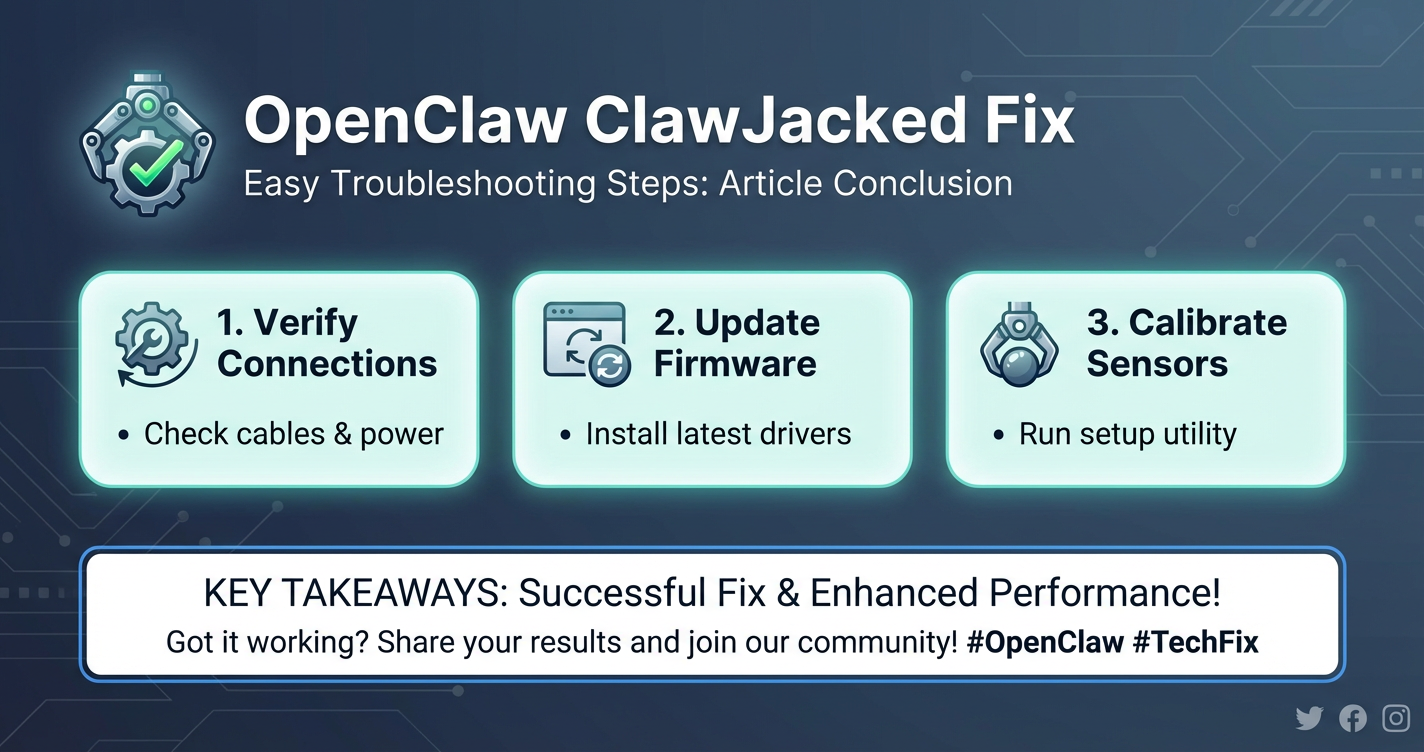
Conclusion
Navigating the complexities of system failures, particularly vexing "ClawJacked" states, can be a daunting experience. However, as this comprehensive guide illustrates, a systematic and methodical approach is your most potent weapon. From the initial frantic moments of an outage to the calm, analytical process of root cause identification and solution implementation, every step plays a crucial role in restoring stability and preventing future disruptions.
We've covered the spectrum from defining the elusive "ClawJacked" symptoms and their myriad root causes—ranging from subtle software bugs and configuration mishaps to resource exhaustion and security vulnerabilities. We then explored structured diagnostic techniques, emphasizing the critical role of logs, resource monitoring, and network verification. Our deep dive into fixes illuminated strategies for correcting configurations, managing dependencies, optimizing performance, and safeguarding data integrity—all critical for a robust OpenClaw system.
Furthermore, we delved into advanced troubleshooting, recognizing that persistent issues might stem from security breaches or intricate API integration challenges, where robust API key management is paramount. We also highlighted the immense value of collective knowledge through community engagement and vendor support.
Crucially, the journey doesn't end with a fix. The most effective strategy is always prevention. By adopting proactive measures such as regular maintenance, robust monitoring, comprehensive automation, and intelligent cost optimization, you transform a reactive crisis management posture into a proactive resilience strategy. Tools and platforms like XRoute.AI exemplify this forward-thinking approach, simplifying complex API key management and offering cost-effective AI access, thereby mitigating common sources of "ClawJacked" issues in modern, AI-powered applications.
Ultimately, mastering the "OpenClaw ClawJacked Fix" isn't just about troubleshooting a specific problem; it's about cultivating a mindset of continuous improvement, vigilance, and strategic planning. By understanding your OpenClaw system intimately, embracing best practices, and leveraging the right tools, you empower yourself to build and maintain systems that are not only functional but also resilient, efficient, and secure, ensuring smooth operations and sustained success in an increasingly complex digital world.
Frequently Asked Questions (FAQ)
Here are some common questions regarding "ClawJacked" issues and general system health:
1. What is the very first thing I should do if my OpenClaw system goes into a "ClawJacked" state? The immediate first step is to stay calm and verify the scope. Check if the entire system is down, or just a specific component. Then, quickly review recent logs for any immediate error messages or warnings, and check basic resource utilization (CPU, memory) to see if anything is immediately spiking. A cautious restart of the affected component might be attempted if logs don't immediately reveal a critical issue and the impact of a restart is understood.
2. How can I distinguish between a performance bottleneck and a complete system failure when troubleshooting a "ClawJacked" issue? A performance bottleneck usually manifests as extreme slowdowns, high latency, or unresponsive behavior under load, but the system or application is still technically running and processing (albeit slowly). A complete system failure, conversely, involves crashes, services failing to start, or total unresponsiveness, where no operations are being processed. Monitoring tools showing high resource usage (CPU/memory) and high queue depths often point to bottlenecks, while outright error logs and service status checks indicate failures.
3. What are the key strategies for "Performance Optimization" that can prevent future "ClawJacked" incidents related to resource exhaustion? Key strategies include implementing effective caching (application, database, CDN), optimizing database queries with proper indexing and efficient design, leveraging asynchronous processing for long-running tasks, distributing load with load balancers, and ensuring code is optimized for efficient resource use. Regular profiling and load testing are crucial to identify and address bottlenecks proactively.
4. How does "Api key management" directly contribute to preventing "ClawJacked" scenarios, especially when integrating with external services like LLMs? Poor API key management can lead to "ClawJacked" scenarios in several ways: exposed keys can be misused, leading to rate limit breaches or unauthorized actions; expired or revoked keys cause authentication failures; and using a single key for multiple services/environments increases the blast radius if compromised. Proper API key management (secure storage, rotation, least privilege, granular permissions) ensures reliable, secure, and uninterrupted communication with external APIs, preventing these common points of failure. Platforms like XRoute.AI further streamline this by centralizing access to multiple LLM APIs through a single, managed endpoint, simplifying security and reliability.
5. Besides preventing "ClawJacked" issues, how can proactive measures like monitoring and automation also contribute to "Cost Optimization"? Proactive monitoring helps identify underutilized resources that can be scaled down, directly saving infrastructure costs. Automation, particularly through auto-scaling and serverless architectures, ensures that you only pay for the resources you actually consume, dynamically adjusting to demand. By preventing outages, you avoid the significant hidden costs of downtime, incident response, and reputational damage. Furthermore, efficient resource allocation through consistent configurations (IaC) and optimized API usage (e.g., via XRoute.AI's flexible LLM access) ensures you get the most value for your spend.
🚀You can securely and efficiently connect to thousands of data sources with XRoute in just two steps:
Step 1: Create Your API Key
To start using XRoute.AI, the first step is to create an account and generate your XRoute API KEY. This key unlocks access to the platform’s unified API interface, allowing you to connect to a vast ecosystem of large language models with minimal setup.
Here’s how to do it: 1. Visit https://xroute.ai/ and sign up for a free account. 2. Upon registration, explore the platform. 3. Navigate to the user dashboard and generate your XRoute API KEY.
This process takes less than a minute, and your API key will serve as the gateway to XRoute.AI’s robust developer tools, enabling seamless integration with LLM APIs for your projects.
Step 2: Select a Model and Make API Calls
Once you have your XRoute API KEY, you can select from over 60 large language models available on XRoute.AI and start making API calls. The platform’s OpenAI-compatible endpoint ensures that you can easily integrate models into your applications using just a few lines of code.
Here’s a sample configuration to call an LLM:
curl --location 'https://api.xroute.ai/openai/v1/chat/completions' \
--header 'Authorization: Bearer $apikey' \
--header 'Content-Type: application/json' \
--data '{
"model": "gpt-5",
"messages": [
{
"content": "Your text prompt here",
"role": "user"
}
]
}'
With this setup, your application can instantly connect to XRoute.AI’s unified API platform, leveraging low latency AI and high throughput (handling 891.82K tokens per month globally). XRoute.AI manages provider routing, load balancing, and failover, ensuring reliable performance for real-time applications like chatbots, data analysis tools, or automated workflows. You can also purchase additional API credits to scale your usage as needed, making it a cost-effective AI solution for projects of all sizes.
Note: Explore the documentation on https://xroute.ai/ for model-specific details, SDKs, and open-source examples to accelerate your development.